Secure Your Productivity and Supply Chain
Sagacent Technologies cybersecurity and co-managed services protect your business, productivity, reputation, supply-chain partners, and more.
IT is essential to modern manufacturing. From customer data and intellectual property to control processes and supply-chain interactions—keeping your IT running optimally and safely is key for manufacturing companies of all types and sizes.
That’s why Sagacent Technologies offers you co-managed and cybersecurity services that optimize the performance of this key asset.
Cybersecurity You Can Count On
In today’s connected economy, it’s increasingly likely that your business will get hacked—especially if you’re not prepared.
Can You Afford the Business Impacts?
After a cyberattack, it takes an average of 277 days for security teams to identify and contain a data breach, according to “Cost of a Data Breach 2022,” a report released by IBM and Ponemon Institute. During this time period, your manufacturing company could:
- Lose suppliers and customers
- Suffer damage to your reputation
- Lose data, including intellectual property, financial, and customer information
- Be locked out of access to computers, servers, or production equipment
- Have to pay ransomware payments of hundreds of thousands of dollars
- Find it difficult or expensive to get insurance
How To Build Better Security
To protect your business against the problems cyberattacks can cause, you need to both guard against hackers and have plans to mitigate any potential damage they might cause.
Sagacent Technologies has an easy three-step process to get you on the path toward securing your business and valuable assets:
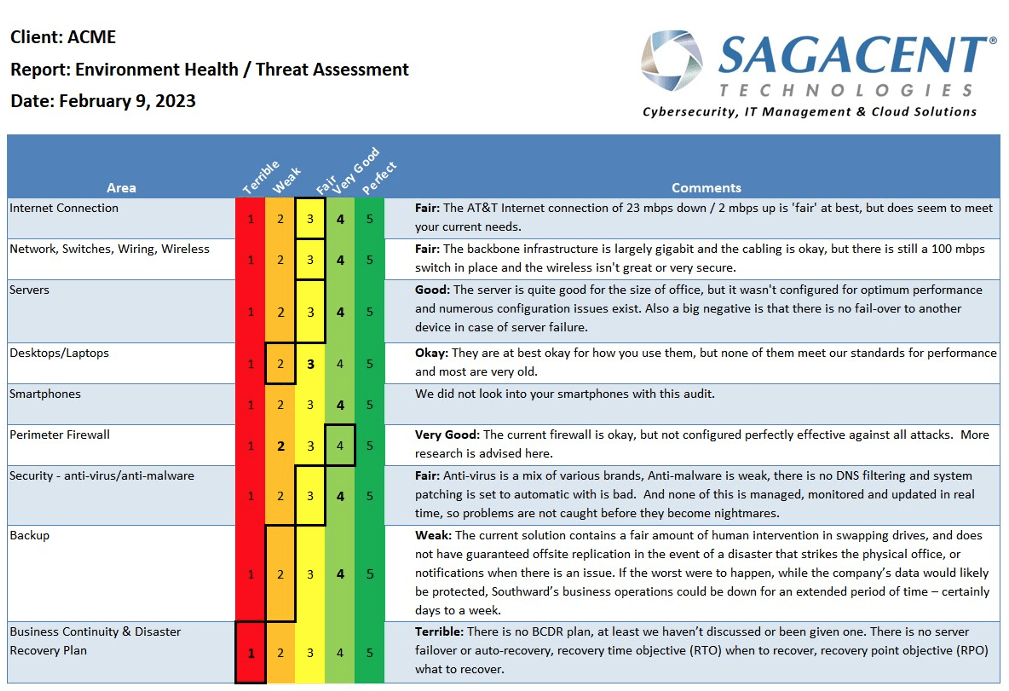
- A cybersecurity assessment shows you the gaps that can make you vulnerable.
- An implementation plan puts your new knowledge into action by working with our experts to ensure that all workflows, internal policies, and initiatives align with security frameworks and regulations for manufacturing.
- A professional backup and recovery plan makes you less vulnerable to ransomware and possible business downtime.
Taking these actions will help you avoid fines for not complying with security regulations, can qualify you for contracts with government providers and other prospective customers who want to ensure supply-chain cybersecurity. It will also help you qualify for cybersecurity insurance at better rates.
Co-managed Services for Peak Performance
Manufacturing businesses, because they are generally subject to so many extra-business guidelines and “must-have” procedures, tend to benefit greatly from remote expert professional services. As a third-party contractor, Sagacent Technologies lets you keep your highly trained onsite IT staff for rapid-response hardware support, onboarding, and moves; while getting expert, remote support in specialized areas such as compliance and cyber security and adding a number of business benefits:
- Complete services—With managed or co-managed services from Sagacent, you get management, maintenance, monitoring, support, and security for your IT infrastructure.
- A proactive approach—We monitor multiple aspects of your IT infrastructure (servers, computers, network etc.) and prevent the failures before they occur.
- A flat-rate fee with no surprise costs—We handle most services remotely, but we can dispatch a technician or if you need a hardware upgrade, we can supply hardware to you and install it at no additional fees. And your whole team can contact our help desk whenever they need support.
- Customized services—Whether you have in-house IT services and need to supplement them with co-managed services, or need full IT support with managed services, you can benefit from the experience and expertise of the Sagacent team.
Get an Assessment of Your Cybersecurity Risks
For the most comprehensive, layered security solutions, fill out the form to request your free Sagacent security assessment.
Secure Your Supply Chain

While today’s digitized supply chains are more efficient, they also leave the entire chain vulnerable to cybercriminals who can steal a wide variety of information, interrupt production, and create more opportunities for damage in a computerized network—putting all parties at risk.
Because of this, more and more customers are expressing concern about cybersecurity (or the lack of it) in the digital ecosystem, and they are making business decisions based on those concerns.
Manufacturing Is a Prime Target

Though large companies that are hacked get the most coverage, hackers sometimes prefer smaller companies because they assume their security will be weaker. Also, smaller companies are understandably reluctant to report attacks for fear of reputational damage, but enough companies do report hacks to show that these kinds of cyberattacks are accelerating.
And the damage can be significant. IBM and the Ponemon Institute report that it takes an average of 277 days for security teams to identify and contain a data breach.
IT Transformation vs. Belt-tightening During a Recession

If you buy into the idea that recessions create opportunities to rethink and transform your SMB, riding out the storm and positioning for a strong recovery, what are some practical ways to do that?
Let’s assume that you’ve decided to focus on Information Technology because of its high cost and importance to your business.